This week I was in the market for two new computers for my kids. The ones they had been using were getting a little long in the tooth and it became apparent that we needed to replace them. This went from annoyance to emergency as they started school again and virtually needed to do classwork. So, I set off on my weekly trip to Costco where you can conveniently buy fruit, t-shirts, pretzels, and yes… computers. So, I bought two decent laptops that would fit their requirements just fine. With that and some extra bottles of wine (more on that later), I returned home.
I plugged in the computers and simple enough, logged into the computer with our family address, which pulled down the settings in Windows 10 and we were off to the races. I installed a few applications they use and then went to check the security and patch configuration. I immediately saw that the security center was showing an exclamation mark. Why, might I ask does a brand new computer not show a healthy security status once fully patched? Upon investigation I found that the computer was running McAfee Security software (SafeLife). Years ago, before Microsoft had an excellent security platform already installed on Windows 10, I’d have needed to break down and install an AV software on the laptops (I still wouldn’t have chosen McAfee BTW), but Windows has AV BUILT IN, which is now DISABLED for a 30-DAY-TRIAL of McAfee, which will leave my computer UNPROTECTED in 30 DAYS rather than just leave the computer always protected by itself. Why, in this day and age am I still putting up with PC vendors needing to make a buck by installing junk I don’t need, especially in the security department where we need individuals as safe as possible. How many people purchasing their brand new HP computer from Costco has been tricked into paying for McAfee because they didn’t know they could just uninstall it and have a protected computer for FREE? Well… that’s what I did and I’m happier or richer for it.
Well, McAfee, you’re so vain, you probably think this blog is about you… it’s not… at least not directly. What this is about is SIMPLICITY. We’ve all heard the term “keep it simple stupid”. There’s another one… the secret of systems integrators is “don’t integrate systems” (unless its the only way). Why? Because simple is better. If I can do 80% or even 100% of the job in a simpler model, it will be more understandable, more supportable, and a better experience. Let’s think about this same story in the corporate context of Zero Trust.
Lateral Movement
In the corporate environment there are two common security scenarios we see time and time again. Randomware and Targeted Attacks. These represent the most likely patterns that a company needs to protect themselves from. The good (or bad) thing is that both have a common pattern used to take advantage of the environment… lateral movement. The compromise of identity, to end user computing, to server, to another server, to critical database can be used to steal important information, or compromise the entire environment with Ransomware.

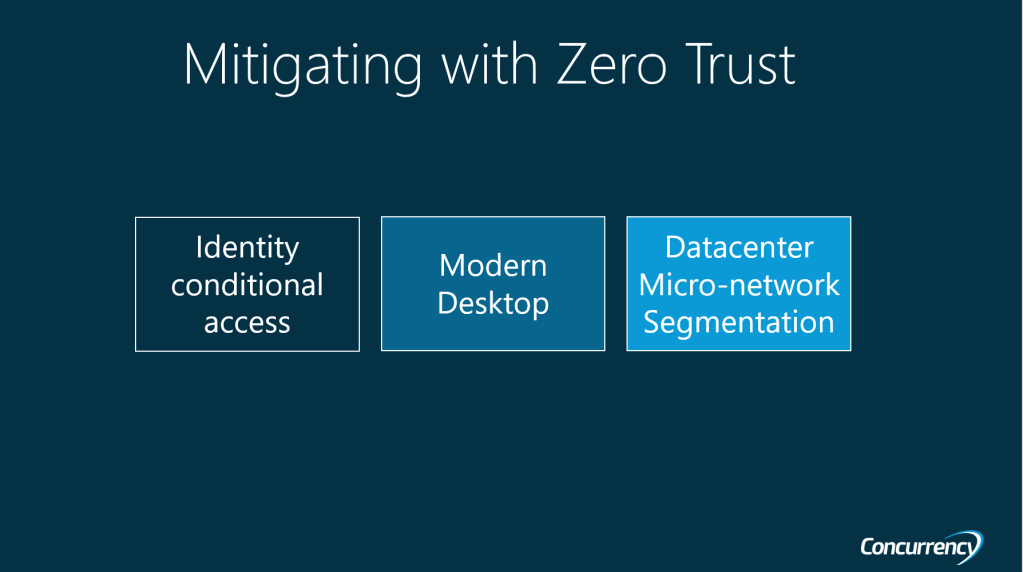
Mitigating with Zero Trust
There are three keys to mitigating the most common security challenges in a corporate environment. They are to contain the identity perimeter with conditional access, invest in modern desktop (get PCs off the network), and data center micro-network-segmentation. These combined with a trust no one (thanks X-Files) create a clear north star for the Zero Trust onboarding activities.
Corporation 1: Best of Breed Workplace
The first business selects a series software they believe to be “best of breed” (or so they think). There are many combinations, but it typically resembles an “anything but Microsoft” workplace environment. Much of the diversity of tools is caused by silos within the organization wanting their own tool for each function. Each function tries to perform its purpose, but the benefits of integration are lost because the tools don’t talk natively. The antivirus software, threat software, identity, conditional access, CASB, etc. don’t talk with each other in a kill chain. The result is a lot of work spent on individual siloed security efforts or trying to get these tools to talk with each other to accomplish a common purpose. Often more effort is spent on the incident management process being well organized to these groups can be brought together, rather than try to integrate. Can this deliver on security? Yes, but it’s a hell of a lot of work. Silos are good for storing grain, not for security operations.

Corporation 2: Simple Secure Modern Workplace
The second company looked at end user computing as a commodity. What is the easiest way to deliver a secure modern workplace? How about if the identity, device, and application all talked to each other within the same platform? This is what you already get with Microsoft 365 E5 (not to mention E3). The idea that if a device is unhealthy, the user can’t use the device (or their login) to authenticate to the SaaS application because the platform contains the entire (or more) of the kill-chain allows a simpler solution to accomplish more faster. Some would say Microsoft misses some features here or there (not saying that is true or not), but if I can get 100% of 80% deployed, that’s a lot faster than 20% of 100%. I get more, faster, and with less work from my team.
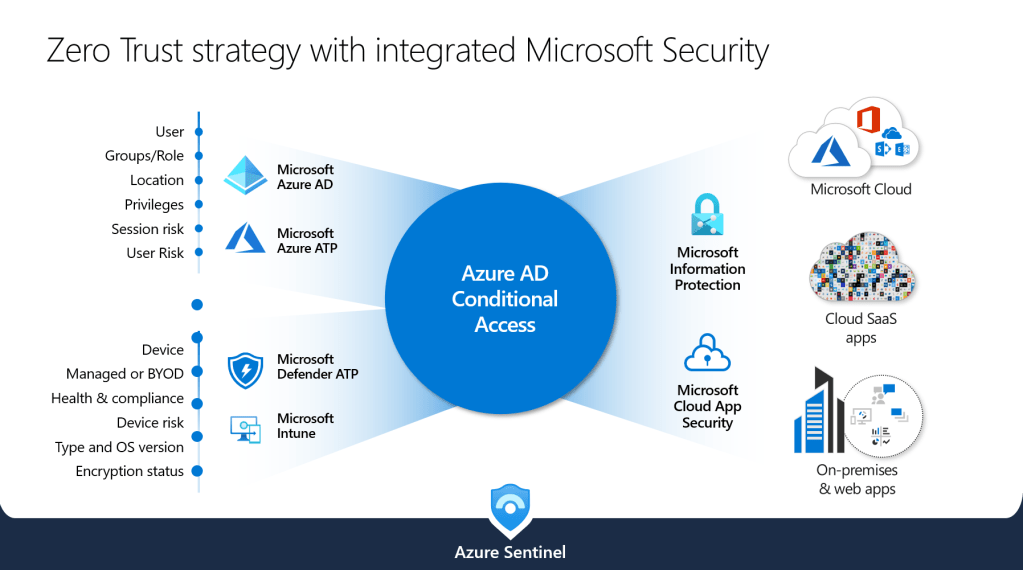
An example of this kill-chain below, where the healthy user is using an unhealthy device and we then block access. The capability of combining the kill chain without having to integrate products is HUGE:

Bringing it All Together:
Let’s go back to our original conversation about buying the laptop from Costco. What could they have done better? Provide a simple user experience, use out-of-box capabilities, don’t require additional investment by layering on useless products. This would have brought a much simpler experience to the user and they would have had a better outcome. If this is mapped to a corporate scenario it is the transition to Modern Desktop. The Modern Desktop story accomplishes a simple user experience (unbox and go) in conjunction with architectural changes by implementing Zero Trust through a desktop operating as a non-trusted device that is validated through the steps we talked about above. See the difference in the Modern Desktop vs. the Legacy Desktop below.

The core message is that simple is better for both the customer and the security kill chain. If you consider the importance of mitigating security threats immediately when they occur, in conjunction with the expectation that end users have with the commodity of technology, concepts like Modern Desktop and Conditional Access are absolutely critical. You then combine these with the transformation of the datacenter, you arrive at a truely different security paradigm that architecturally addresses many of the gaps in the modern threats. Like the old saying goes… KEEP IT SIMPLE STUPID.
Nathan Lasnoski